SnailLoad
Remote Network Latency Measurements Leak User Activity
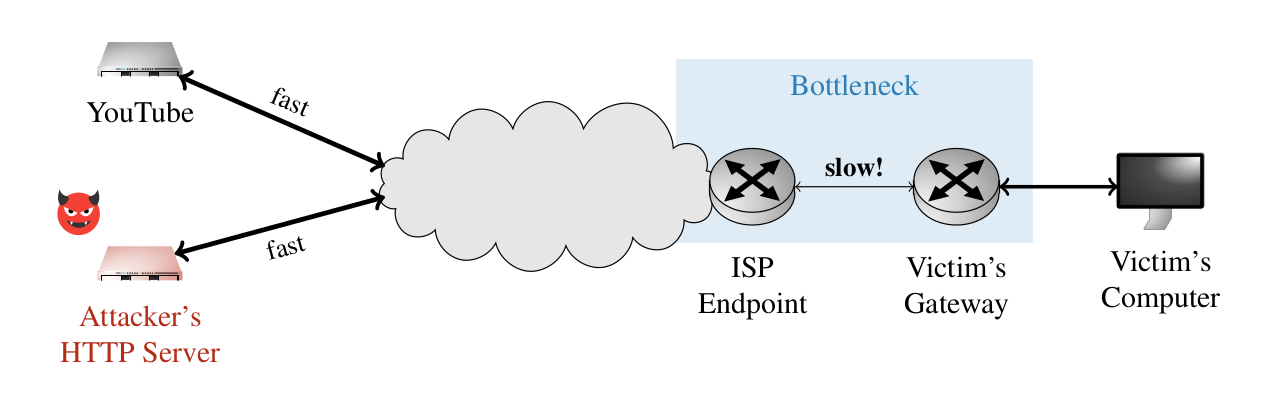
SnailLoad exploits a bottleneck present on all Internet connections. This bottleneck influences the latency of network packets, allowing an attacker to infer the current network activity on someone else's Internet connection. An attacker can use this information to infer websites a user visits or videos a user watches.
SnailLoad Attack Setup:
- The victim communicates with a server.
- The server has a fast Internet connection, the victim's last mile connection is comparably slow.
- The attacker's packets to the victim are delayed if the last mile is busy.
- In a side-channel attack the attacker infers what website or video the user is watching.
Who is behind SnailLoad?
SnailLoad was discovered and reported by a team of researchers from Graz University of Technology:
- Stefan Gast
- Roland Czerny
- Jonas Juffinger
- Fabian Rauscher
- Simone Franza
- Daniel Gruss
Questions & Answers
Am I affected by this bug? Should I worry?
We believe that most Internet connections are affected. However, at this time it is unlikely that SnailLoad is exploited in the wild. SnailLoad exploits bandwidth bottlenecks close to your device. Typically, the bandwidth bottleneck is your personal internet connection, as it has a much lower bandwidth than backbone infrastructure. Our user-study with 10 home internet connections shows that our video-fingerprinting attack works on all of the tested connections, with varying accuracies between 37% and 98%.
My router does not respond to pings, am I safe?
No, because TCP ACKs carry the same information.
Why can't we disable TCP ACKs?
ACKs are fundamental for reliable data transmission via TCP. When transmitting TCP packets, the sender expects the receiver to send ACKs to confirm that the packet arrived. This ensures that packets are retransmitted if they are lost. Removing the ACK mechanism from the TCP protocol would effectively remove its reliability guarantee and hence its core feature. Apart from that, changing the behavior of an ubiquitous protocol like TCP is just impractical for compatibility reasons.
What about mitigations?
Mitigating SnailLoad is not trivial. The root cause of SnailLoad are bandwidth differences between backbone and end-user connections. To provide a suitable bandwidth to multiple users simultaneously, the backbone network infrastructure has to have a higher bandwidth than the connections of the individual users. Hence, the root cause cannot be eliminated and further research is necessary to find satisfying solutions.
Why is it called SnailLoad?
The attack masquerades as a download of a file or any website component (like a style sheet, a font, an image or an advertisement). The attacking server sends out the file at a snail's pace, to monitor the connection latency over an extended period of time. Apart from being slow, SnailLoad, just like a snail, leaves traces and is a little bit creepy.
What is CVE-2024-39920?
CVE-2024-33920 is the official reference to SnailLoad. CVE is the Standard for Information Security Vulnerability Names maintained by MITRE.
Can I use the logo?
The logo is free to use, rights waived via CC0.
Is there proof-of-concept code?
We released our basic SnailLoad example server on GitHub.
Acknowledgements
We would like to thank our anonymous reviewers and our shepherd for their valuable and timely feedback. We furthermore thank David Bom, Lukas Maar, Sebastian Felix, Andreas Kogler, Lorenz Schumm, and Martin Glasner. This research was supported in part by the European Research Council (ERC project FSSec 101076409) and the Austrian Science Fund (FWF SFB project SPyCoDe 10.55776/F85 and FWF project NeRAM I6054). Additional funding was provided by generous gifts from Red Hat, Google, and Intel. Any opinions, findings, and conclusions or recommendations expressed in this paper are those of the authors and do not necessarily reflect the views of the funding parties.